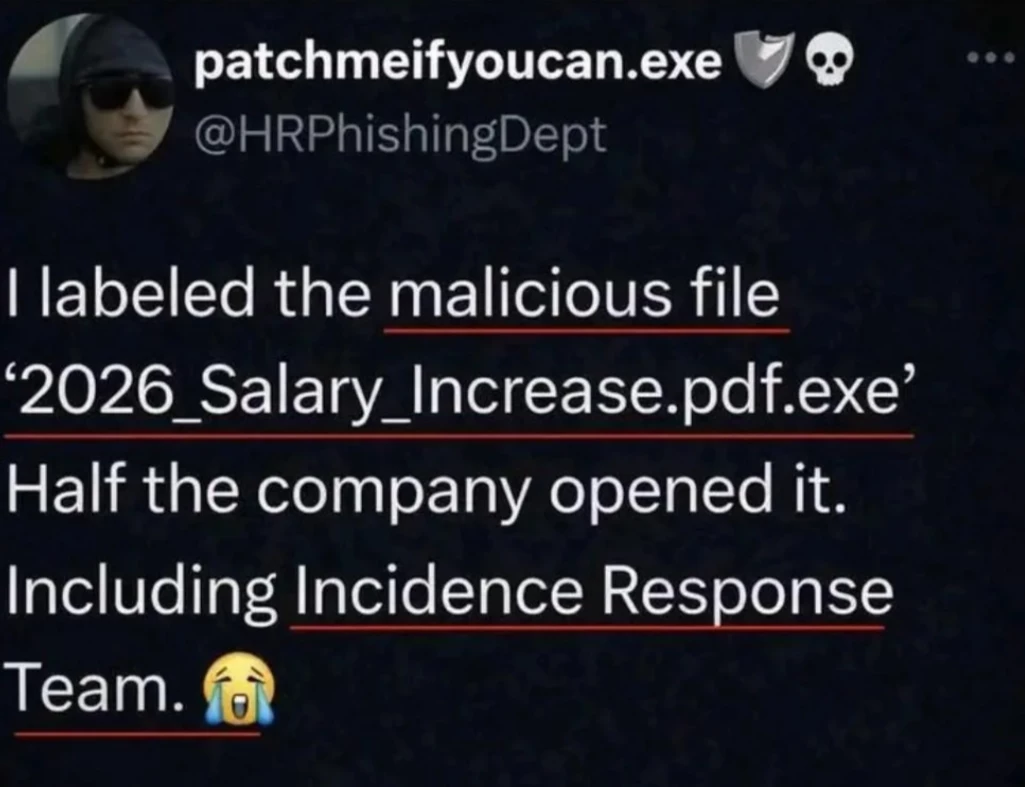
A malicious file labeled “2026_Salary_Increase.pdf.exe” was opened by a large portion of employees — including the Incident Response team.
Let that sink in.
This isn’t about lack of intelligence. It’s about how easily human psychology can be exploited:
Curiosity (salary increase)
Urgency (what if I’m missing out?)
Trust in familiar file naming patterns
Key takeaways for teams:
• File extensions still matter — .pdf.exe is a red flag
• Security awareness training must be continuous, not one-off
• Even security teams need realistic phishing simulations
• Technology alone won’t save you — behavior will
The real vulnerability isn’t the system. It’s the assumption that “this wouldn’t fool me.”
When was the last time your organization tested this?
#CyberSecurity #Phishing #SecurityAwareness #InfoSec #QA #RiskManagement